Anthropic's Mythos Model Reveals Thousands of Critical Software Bugs Before Public Launch – Firefox Security Researchers Detail Impact
By admin | May 07, 2026 | 5 min read

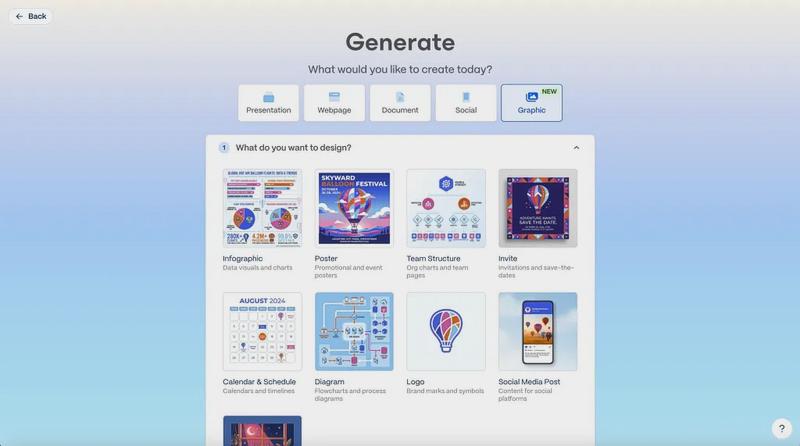
When Anthropic introduced its new Mythos model in April, it also issued a strong caution to software developers everywhere. The lab claimed the model was exceptionally adept at detecting software vulnerabilities, uncovering thousands of high-severity bugs that required fixes before the model could be released publicly. Now, security researchers from Mozilla’s Firefox browser are offering a detailed look at how this process has unfolded in practice and what Mythos’ capabilities mean for software security overall. In a post published on Thursday, Mozilla stated that Mythos has discovered numerous high-severity bugs, including some that had remained hidden in the code for over a decade. This marks a substantial leap forward from what AI security tools could achieve just six months ago. Previously, AI bug-finding tools had significant drawbacks, often overwhelming security teams with low-quality reports and false positives. However, Mozilla’s researchers note that the latest generation of tools has reached a turning point, especially now that agentic systems can evaluate their own work and eliminate poor results. “It is difficult to overstate how much this dynamic changed for us over a few short months,” the researchers wrote. “First, the models got a lot more capable. Second, we dramatically improved our techniques for harnessing these models.”

The outcomes are impressive: In April 2026, Firefox shipped 423 bug fixes, compared to just 31 in the same month a year earlier. The researchers have also shared details on 12 of these bugs, which include two unusual sandbox vulnerabilities and a 15-year-old error in how the browser parses an HTML element. “We see that on our own internal scanning, we see that on external bug reports, and we see that in all sorts of signals across the industry.”
The system’s ability to uncover vulnerabilities in Firefox’s “sandbox” system is especially noteworthy, given the complexity of exploiting such a flaw. To find sandbox vulnerabilities, the model must craft a compromised patch for the browser and then attack the most secure part of the software with the new code implemented. Identifying and demonstrating the bug requires a delicate, multi-step process that demands both creativity and meticulous attention. For context, Mozilla’s bug bounty program offers up to $20,000—the highest reward available—for researchers who can find a bug in Firefox’s sandbox. Despite this top-dollar incentive, Grinstead says Mythos is discovering more sandbox issues than human researchers ever did.
Notably, the Firefox team is still not using AI to fix the bugs, despite significant progress in AI coding tools. The team does ask AI to generate patches for each bug, but the resulting code typically cannot be deployed directly and instead serves as a template for a human engineer. “For the bugs we’re talking about in this post, every single one is one engineer writing a patch and one engineer reviewing it,” Grinstead says. “We have not found it to be automatable.”
It remains unclear how AI’s emerging capabilities will reshape the broader balance of power in cybersecurity. One month after Mythos was previewed, most of the discovered bugs have likely not been patched, making it difficult to fully assess their impact. Anthropic has been careful to follow responsible disclosure norms, but it’s likely that malicious actors are using similar techniques behind the scenes, even if their models are not as advanced. Speaking at a recent event, Anthropic CEO Dario Amodei expressed optimism that the new tools would ultimately benefit defenders. “If we handle this right, we could be in a better position than we started, because we fixed all these bugs. There are only so many bugs to find,” Amodei said. “So I think there’s a better world on the other side of this.”
Having dealt with the practical realities, Grinstead offers a more cautious perspective: “It’s useful for both attackers and defenders, but having the tool available shifts the advantage a little bit to defense. Realistically, nobody knows the answer to this yet.”
Comments
Please log in to leave a comment.


No comments yet. Be the first to comment!